It’s great to hear from readers, and we have had a couple of timely questions from some of you.
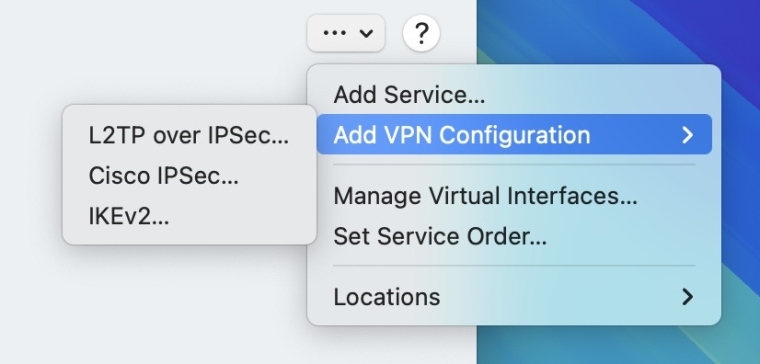
The first one from NR is about whether or not to use a virtual private network or VPN. If VPN is a new term and abbreviation, it refers to a network technology that sets up an authenticated and encrypted “tunnel” between your computer (or smartphone), and another machine elsewhere, for data transmission.
In simple terms, network endpoints find each other with Internet Protocol (IP) addresses. Using a VPN means the IP address allocated to your device isn’t publicly visible. Instead, it appears to systems on the Internet as if your IP address is that of the VPN endpoint.
A VPN doesn’t anonymise you, but it can be a very useful tool. It would be very difficult to break the VPN encryption to intercept the data going through the tunnel to read or tamper with it.
There are times when you want to bypass “geofencing” which is the technology used to locate where you are. It can come in handy for, say, network troubleshooting, as you can make your computer in New Zealand appear as if it is in a different country altogether.
Many people use a VPN to access digital content that’s blocked in one country, which can be illegal depending on the jurisdiction you’re in. Tunnelling out of that dodgy public Wi-Fi network that’s open to all and sundry in that downtown cafe with a secure VPN is not a bad idea in general, although, if you have to go through an unencrypted captive portal first, it's better to hotspot off your telco 4G/5G data instead.
VPNs aren’t guaranteed to always work. A business trip some years ago to China required the use of multiple VPNs, in order to be able to work with systems outside the country’s heavily censored Internet which blocked access to them by default. Although it couldn’t crack the encrypted traffic, the “Great Firewall of China” would after a few days learn what your VPN traffic looked like. Once that happened, the GFC blocked the traffic stream. So you fired up another VPN, and kept going until that too was blocked. This was done on the advice of my Chinese hosts by the way.
There are several other uses for VPNs, and I trust the comments section will supply further interesting examples.
Using VPNs isn’t without risks. The obvious one is that you need to know and trust the VPN operator you use. Unfortunately, lots of shady operators offer malicious “free” apps that record user and traffic information. A few years ago, Australians flocked to VPNs in large numbers to bypass blocks on different sites.
Unfortunately, enterprising digital criminals had laid a minefield for users downloading VPN apps, and embedded malware into an alarming number of these. Installing a malicious app could lead to your entire device with the information stored on it being compromised. A great deal of care is required if you use a VPN application from a third party provider, in other words.
Do you need a VPN? In most cases no. Since the Internet is such hostile ground these days, software developers have worked hard to encrypt as much data traffic as possible to keep it secure. A flip side of using a VPN is that your network speeds are likely to drop, depending on how the traffic is routed and server/link capacity.
It’s more important to focus on keeping your software up to date and secure, and developing an understanding of common Internet-borne threats like phishing and unexpected friend-making requests on Facebook. Learn how to make life more difficult for cyber criminals with multi-factor authentication and just be careful out there.
If you take your time to understand what VPNs can and can’t do, and pick reputable operators - which can be difficult, they are a handy addition to the Internet User’s tool kit.
Kaspersky cops king hit in the US
Another question that arrived was “is Kaspersky OK?” as in using the security software. That’s a topical one, as the security vendor has been in the news recently.
To start with, you cannot talk about anti-viruses and IT security without mentioning Kaspersky. It’s one of the “original gangstas” of the infosec business, set up in 1997 by the then-couple Natalya and Eugene Kaspersky, in Moscow, Russia.
Over the years, Kaspersky Labs has unearthed much malware and multiple threat actors, earning kudos and respect in the process from the infosec industry. Some of the research done by the company, and published on the Threat Post blog has been excellent.
None of which can deflect from the fact that being a Russian company currently, albeit one with important parts of its operations shifted to Europe, is guaranteed to lead to allegations of collusion with Putin’s intelligence services.
Kaspersky Labs strenuously denies all the allegations, but Russia’s recent actions, particularly the war against Ukraine, has turned “Сделано в Российской Федерации” into a full-blown liability. Nobody at Kaspersky Labs can be surprised at that.
The security vendor’s products have been banned from official IT systems in the European Union, and the United States, where first the Trump administration and then the Biden administration have limited Kaspersky Labs’ business.
Now, Kaspersky Labs has been hit with a sales ban in the US, including for private use, for being a threat to national security.
This is very much next level by the American authorities, a first of its kind ban. It also includes updates for Kaspersky’s anti-virus/anti-malware utilities.
What’s more, the US Treasury’s Office of Asset Control (OFAC) has sanctioned Kaspersky members of the company’s executive team and senior leadership. Not Eugene Kaspersky himself, but much of the security vendors' senior management are listed and will find life more difficult from now on.
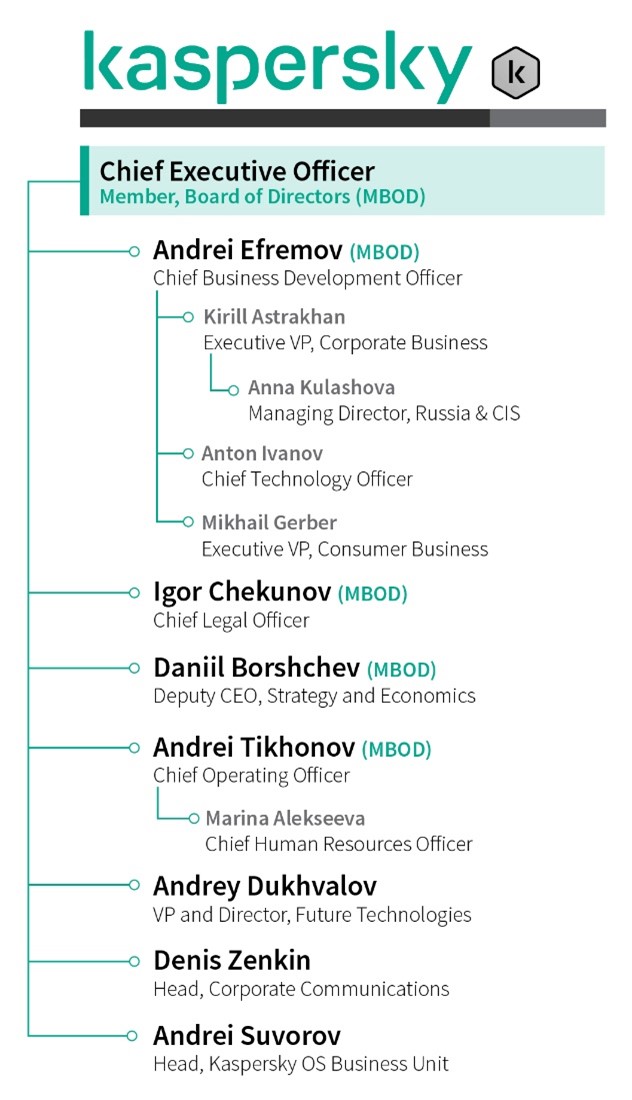
Kaspersky will also find it difficult to get paid thanks to the sanctions. Again, as Putin and cronies cosy up to North Korea, commit heinous war crimes in Ukraine and issue nuclear threats, the issues brought on by being a Russia-associated company can’t be news to Kaspersky.
Let’s just say that if you haven’t done so already, it would be prudent to look at security products and services from companies that don’t find themselves in the above situation.
Update July 16 2024: Well-respected infosec journalist Kim Zetter reported that Kaspersky is closing its US operations, with staff being let go.
4 Comments
Proton free VPN is perfect for watching tubi TV. You need to be in USA to connect to tubi TV. Proton takes care of that.
With Spotify continuing to increase prices has anyone used a vpn to join Spotify from a $3.95 a month country and just pay by wise or similar?
On using a VPN, I will activate mine whenever I am on a "Free" internet connection, such as those offered in a cafe, airport, hotel, etc.
I maintain this theme for any security related service. Free password managers or free VPN services are simply not worth the risk. Would you install a free alarm or security system in your house? I doubt it, so why treat your personal data carelessly.
Purchase a subscription to a known VPN vender (I use NordVPN) and a pay for a password manager (I use 1Password). Security is not free.
It is hard to understand why connecting through a VPN to a public network would improve security. In general IP connections use transport layer security, which encrypts data and authenticates the server. Provided you connect using https. The headers are exposed but there's not much private information in them, perhaps the IP address and port address of the server. The clients IP address is normally private and can't be used to connect from the outside world. Furthermore on a wireless network a VPN tunnel would not stop another user connecting to and "hacking" a device, if there was a way to do this. The original network still exists. Perhaps VPNs are a way of extracting money from people who think they improve their internet security. They are of course useful in hiding your country of residence as mentioned.

We welcome your comments below. If you are not already registered, please register to comment
Remember we welcome robust, respectful and insightful debate. We don't welcome abusive or defamatory comments and will de-register those repeatedly making such comments. Our current comment policy is here.